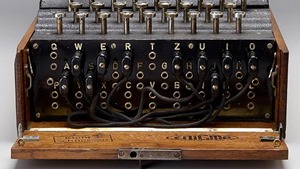
- Zero Trust is a major trend in 2022 and one that affects public and private sector organizations alike. Last year when the Biden administration in the US issued its Executive Order on Improving the Nation’s Cybersecurity, zero trust was a major component of this initiative. Organizations implement traditional perimeter-based security strategies on the assumption that the perimeter is secure inside. Zero trust assumes that no person or device inside or outside of an organization...
- Zero Trust is a major trend in 2022 and one that affects public and private sector organizations alike. Last year when the Biden administration...