Challenges
Protect Intellectual Property (IP)
Companies’ IP cyber-security defenses are crumbling in the face of advanced persistent threats, insider threats, and vulnerable supply chain relationships.
Can you stop the loss or theft of trade secrets and other intellectual property?
Recent numbers cited by government officials place American IP theft at between $225 and $600 billion annually.
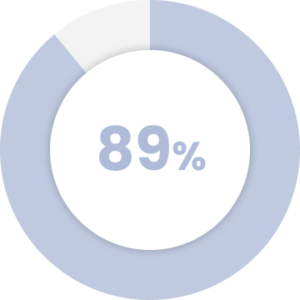
of CISOs believe a fast-paced collaborative culture puts the company at greater risk.
Source: Code42 Data Exposure Report 2019
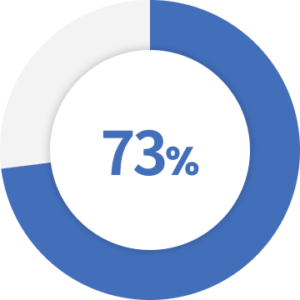
of data breaches take months or years to discover.
Source: Verizon 2019 Insider Threat Report
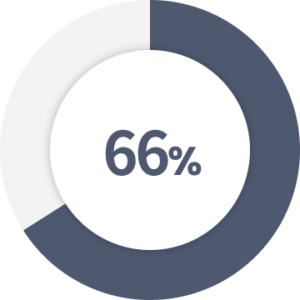
of security professionals identify significant weaknesses with solutions such as DLP, UEBA, and UAM.
Office suite and data loss prevention tools leave enterprise IP vulnerable in many use cases.
Explore the solutions and outcomes for some of the biggest challenges.
Rich IP formats like CAD, engineering drawings, and PDFs are not protected or require an alternative workflow.
Use application-independent solutions to secure all forms of IP.
IP left exposed by traditional solutions is protected without disruption to user workflows.
Authorized at-risk insiders decrypt a document and can use without restrictions.
Apply document rights policies to control data-in-use.
The highest-risk insider threat behavior is controlled and restricted.
IP documents traverse the cloud, endpoints, and third parties, which strip original enterprise controls.
Bind identity policies to the document.
Identity controls are persistently enforced and can be dynamically changed or revoked anywhere.
Key Features
Fasoo Data Security Platform
Fasoo fortifies and scales today’s enterprise infrastructure with strong unstructured data protection and control. Our comprehensive platform is deployed with over 2,000 customers to discover, classify, protect, control, trace, and securely share critical business information.
Discover
Classify
Protect
Adaptive Access
Monitor and Control
Resources

Automotive Parts Manufacturer Protects IP

Fireside Chat: Stop Intellectual Property Theft

Challenges Manufacturing Companies Face

Whitepaper: Fasoo EDRM

Tariffs in the Automotive Industry is not their only concern


