Challenges

How do you protect your endpoints?
Each of your company’s endpoints is a doorway for your employees to access your corporate data. They may use personal devices (BYOD) to access sensitive data, print or take pictures of sensitive documents on the screen, and send them to unauthorized users.
Traditional endpoint protection can’t stop this.
How can you protect your data?
68% of organizations have experienced one or more endpoint attacks that successfully compromised data.
Source: Ponemon Institute
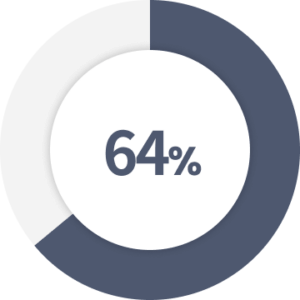
of organizations reported a print-related data loss in the last year.
Source: Quocirca
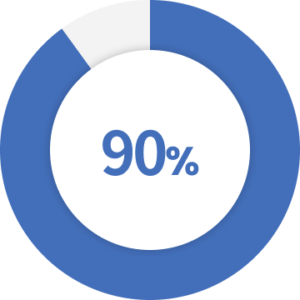
of cyberattacks rely on some form of social engineering.
Source: Security Boulevard

of legal and compliance leaders are concerned about third-party cyber risks due to remote work.
Source: Gartner
Unmanaged personal devices (BYOD), printing, and screens put sensitive documents at increased risk.
Using personal devices (BYOD) and storing sensitive documents.
Assign explicit granular rights to a document to control data in use.
Enforce least privileges and stop unauthorized sharing actions.
Printing sensitive data and sharing it with unauthorized people.
Add watermarks to sensitive documents or prevent the printing of sensitive data.
Minimize the risks of data breaches through printouts.
Capturing sensitive data on a screen and sending it to an unauthorized user.
Add watermarks to sensitive data on the screen or block all screen capture attempts.
Limit and deter data breaches through screen capture attempts.
Key Features


Fasoo Data Security Platform
Fasoo fortifies and scales today’s enterprise infrastructure with strong unstructured data protection and control. Our comprehensive platform is deployed with over 2,000 customers to discover, classify, protect, control, trace, and securely share critical business information.
Discover
Classify
Protect
Adaptive Access
Monitor and Control
Resources

Fasoo Smart Print eBook

How Fasoo Enables Zero Trust Data Security

Fasoo Smart Screen eBook

How to Ramp Up Your Remote Work Document Protection

Document Security: What Is Secure Print?


