How do you mitigate data security and privacy issues in this new AI world?
How do you mitigate data security and privacy issues in this new AI world?
That was the topic of a discussion hosted by Fasoo at the 2023 Gartner Security and Risk Management Summit.
Fasoo CTO and COO Ron Arden spoke with Tad Mielnicki, Co-Founder and COO of Overwatch Data, and Jamie Holcombe, CIO of the US Patent and Trademark Office, about the challenges of using generative AI responsibly.
In Part 1 of this discussion, A Conversation on Risks of Using Generative AI and How to Mitigate Them, we focused on the potential risks of using generative AI and some measures to mitigate them.
During Part 2 of this discussion, Mitigate Data Security Risks When Using AI, the group focused on advice for organizations as they try to navigate and manage the risks of using AI while enjoying the benefits.
In Part 3 of this discussion, we focused on solutions to protect your sensitive data while using generative AI.
*
Ron Arden: So, one last question and then we’ll wrap up. I think we’ve touched upon this a little bit, but what’s the best way for organizations to strike a balance between protecting sensitive information and allowing people to use generative AI?
Jamie Holcombe: My answer is always leadership.
You need a message for using it and a message for disciplined use. And so, you have to strike a balance. That’s about leadership. And you’ve got to inform and educate everyone about it. Don’t be afraid, but be respectful. That’s the way I would do it. Data governance.
Tad Mielnicki: Yeah, use it. If you don’t use it, you’re going to get left behind. That simple. So, you have to use it.
Education is probably the most important thing at the front end. Govern your data properly, but don’t try to stifle advancement. Try to figure out how you’re going to work it into your company, into your workflows. Find in your individual use cases where it’s helpful versus where it’s not.
And don’t be afraid to say we’re not going to use it for this because it’s not optimized in our environment that way. I think it’s fairly straightforward right now. It’s going to get a lot more complicated.
*
Ron Arden: Let’s talk about some additional enhancements. One of the things we’ve been touching upon is the need to monitor what’s going on. In Jamie’s case, some of this is a process. In other cases, you’ve got a lot of data that could be sensitive that’s in the organization, and you want to make sure that it doesn’t get out into a public LLM or other places. One of the ways to do that is intelligent monitoring. Really figuring out what’s going on in the organization.
Use intelligent monitoring to prevent information leaks
Using Enterprise DRM, which is encryption plus policy, is a way to make sure that people can’t inadvertently put your sensitive data into one of these language models. If it’s inside the organization or a public LLM, this is a good way, as Tad mentioned, of governance. And another area that we really didn’t touch too much upon was how do you have security in place to prevent AI-powered attacks. A lot of that is monitoring. It’s a lot of the good hygiene we’ve got today. It’s just with AI it is happening a little bit quicker.
“AI will not replace you. A person or company using AI will.”
I think this is a fantastic quote because a lot of people are worried we’re going to get the Terminator and Skynet and we’ll all be obsolete. I don’t think we’re going to be obsolete, but I think if you as an organization don’t start embracing some of these AI tools, you will be left behind. The genie’s out of the bottle. We’re all using it, it’s going to mature, and the guardrails are going to get there as we go forward.
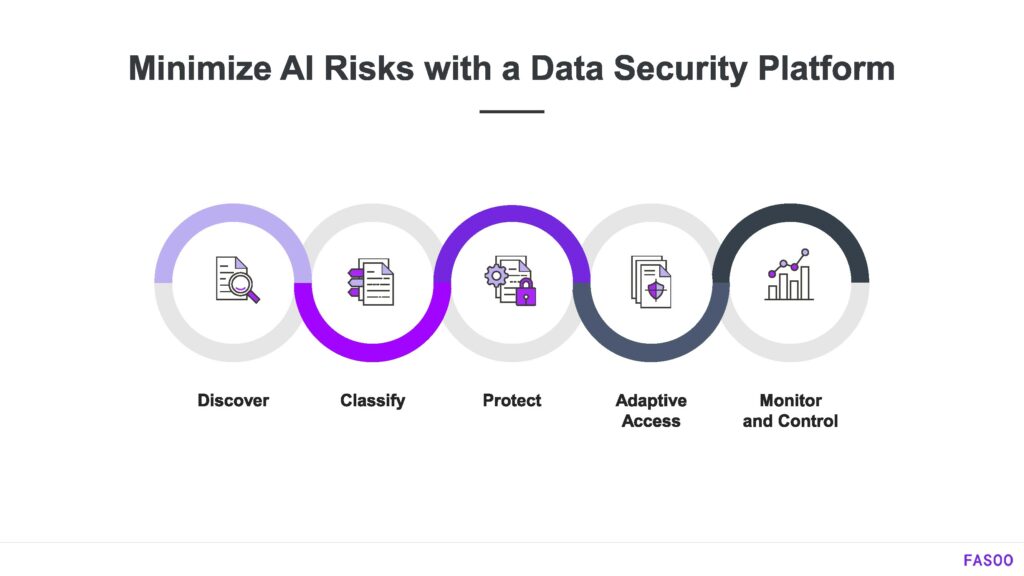
I think it’s just like when the first cell phones came out. It was better than being stuck in the house and it improved over time. So, I think things are going to mature as we move forward. One of the ways that Fasoo addresses this is with our data security platform. And if you think about what we’ve just discussed, I want to govern my sensitive information. I need to look at it, I need to figure out what it is, and I need to tag it in some way so that I can now apply some type of control to it. And then we have to monitor and control it at the end.
We have a fairly robust soup-to-nuts platform that will allow an organization to determine what they have, where it is, and how to govern it.
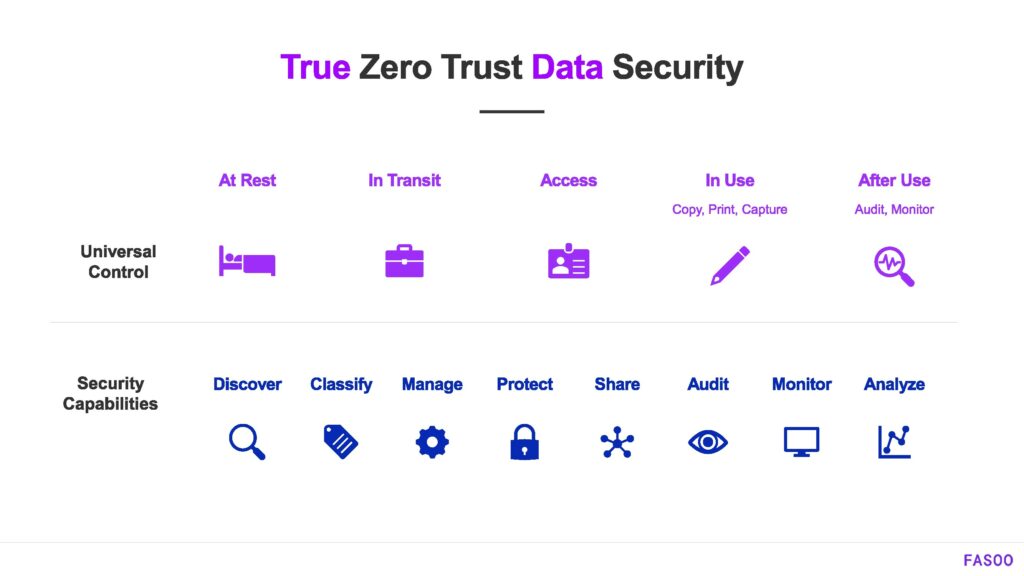
If we look at zero trust for data security, we think about a lot of these elements. Encryption in and of itself, as our head of sales will say, is like a binary solution, it’s on and off.
What you need to do is to govern the access to the data once it is encrypted. And a lot of solutions, from what’s on your laptops to a data center in a cloud, have encryption at rest, and encryption in transit. We’ve been doing this forever since we’ve all used SSL and TLS.
But when I get to open a document and start accessing the data, I need to control that. If I’m inside the organization, I can open that document, but I can’t copy and paste it into the LLM.
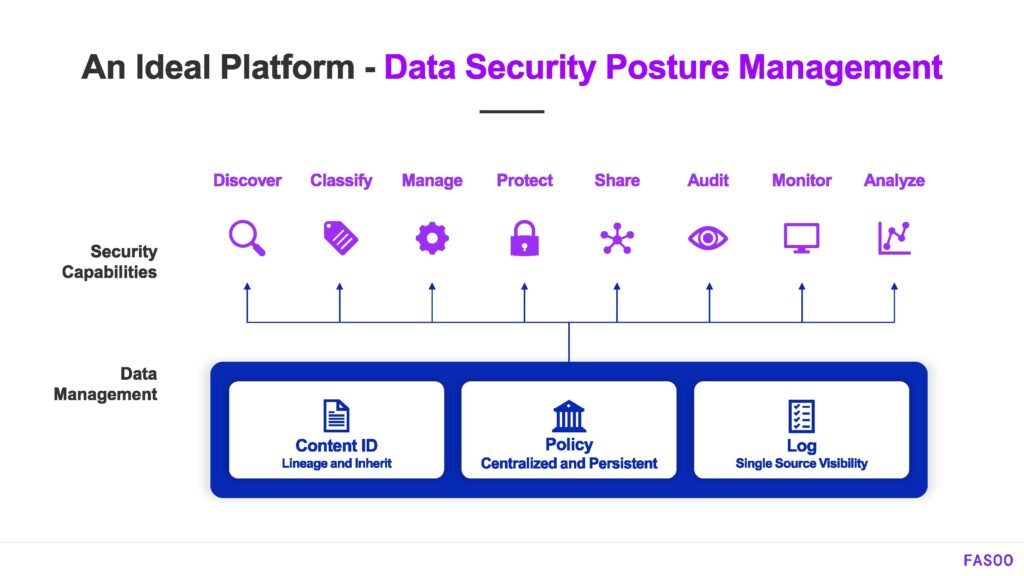
Fasoo has a platform that allows a comprehensive solution throughout the entire data lifecycle to be able to find, protect and manage sensitive, unstructured data.
If you look at the capabilities under the data management layer, we are taking a document, and assigning an identifier to it, which allows you to determine the lineage of that document and all of its derivatives.
If I’m in Jamie’s organization, I’m looking at patents. I’m going to get a document, make a copy, save it as a PDF, and have 100 versions of this out there. I need to be able to control all that data. And then I want to have some kind of a centralized policy management system that allows me to easily govern it.
One of the key things that they said in the keynote this morning is we’ve got to simplify the user experience. If user experience and security are hard, people are just going to find a way around it. So, we want to make sure that a simplified environment exists but is still a secure environment. And then, as somebody said years ago, I can’t prove I did anything until somebody can see that I did something.
I need to have analytics and logs. It’s like the old joke “If the tree fell in the forest, and nobody saw it”. It’s the same thing. If I can’t measure it, it didn’t happen. So that’s a key thing that we have in our platform.
The last thing I want to mention is we, Fasoo, are using AI as well in our tools. We do have a number of solutions that are there to help protect the environment as we are using these AI tools. But like everybody, we’re developing our own language models to use in our products to help protect this data.
Thank you very much. I want to thank the panelists, Tad, and Jamie. It was a very interesting conversation.
*
Most organizations are struggling with how to use generative AI safely while allowing the productivity gains many are seeing. If you want to discuss how Fasoo can help you maintain data security, contact us to talk to an expert.
Click here for a replay of the panel discussion.
###
The transcript of this conversation has been shortened and edited for clarity and the blog format.