According to a recent data breach report by Verizon, 48% of breaches were attributed to people who abused their access rights. That means they had access to confidential information and they stole it or somehow misused it. Most of us think that the majority of problems with data and document leaks are from outside hackers, but a large majority are from people on the inside.
Think about that for a moment. If you are in a large organization, there might be strict rules about what you can access. HR has access to employee information, including salaries and social security numbers (or equivalent national IDs). Finance has access to salary numbers and budgets. IT usually doesn’t have access to this information, although since they manage the systems where the information lives, this is possible. In small organizations, you may not be that strict about divisions of labor, because a few people may wear numerous hats. In my business, I will function as finance, marketing, sales and IT on the same day. That means I am mixing my data access rights.
In these scenarios each group or person is given access to specific information through a username and password. Some organizations use smart cards, biometrics or other security devices, but each is tied to a person. These credentials give the person access to applications or documents which contain the confidential information. The trick is to only give people access to what they need to do their job.
This is a common practice in IT, although not always followed. IT tries to separate administrative tasks from user tasks with separate accounts. This helps to limit user privileges. You should do the same with everyone, including contractors and temporary employees. If someone only needs access to email and the company Intranet, give them only those privileges.
Don’t fall into the trap of giving executives more user rights than they need, just because they are executives. In most cases, the CEO doesn’t need to know my social security number. The same way there are separation of business duties in an organization, such as finance, HR, sales and IT, there should be separation of data and document access privileges. It’s good business and good governance. You should monitor access to confidential information through logs or monitoring tools. These measures won’t solve everything, but a little common sense in these areas goes a long way.
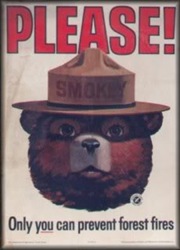
Take a lesson from Smokey the Bear and start looking in the mirror to help reduce data breaches. Start by separating business duties and aligning data and document access privileges to them. Just like locking your front door, it will deter a lot of the trouble.
Photo credit Fennek11

