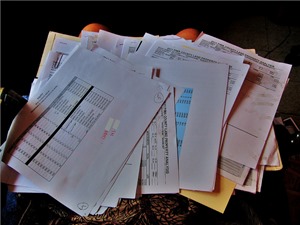
A recent study of more than 1,500 data breaches in 2013 and 2014 by a unit of Beazley P.L.C. reveals that the two most common sources of breaches are unintended disclosure through emails & faxes and the physical loss of paper records. The loss of paper records, which is particularly prevalent among health care organizations, accounted for 24 percent of the total. Interestingly enough, malware and spyware accounted for only 11 percent of the total.
Without proper controls on printing and printing devices, critical documents can be routed in seconds to unauthorized people inside or outside of a business. Printers are easy to overlook when evaluating IT security, as they are often viewed as “dumb” peripherals, but many organizations use intelligent multifunction peripherals (MFPs) which allow users to scan, fax and send email attachments, in addition to simple printing and copying.
Since printers are typically located in common areas with only basic physical security, it is easy for printed information to get into the wrong hands, either accidentally or intentionally. And if an MFP has the
ability to email scanned documents without security measures, it could be used to forward confidential
documents outside the company with no way of tracing the sender.
Applying a dynamic watermark with user information, time, date and company details to a printed document is one way to ensure that you can trace the source of a potential data breach. It may not stop someone from stealing a piece of paper, but it will deter most would be thieves. It’s also important to have an audit trail of who printed what documents and include an image or text of the actual content in your logs. This deters those people who will change the name of a file before printing. A standard print log will only show the current name of the file, but not it’s content. By seeing the actual content, you will know if someone is attempting to steal information.
Requiring a user to enter a pin, swipe a smart card or use a phone app with some authentication to release a print job also protects unintentional or deliberate data breaches. If someone leaves a confidential printout on a printer, anyone could take it. If you have to authenticate at the device before the document prints, you will immediately take your document.
You can also prevent users from printing certain types of documents. If a document is classified as highly confidential, you might restrict it to only certain people inside your organization. I may be able to view the document, but can’t print it. This eliminates the problem altogether since I can’t be the source of a printed leak.
Ensuring a secure printing environment is critical for any organization regardless of its size. For security and compliance, businesses need to identify who uses printing devices, control how they are able to use them and gather accurate usage audits. In today’s digital world, minimizing security risk and protecting confidential information has become a top priority and protecting your printing environment is a critical part of your information security.
Photo credit Raquel Baranow

