This is not a surprising finding since large and small organizations alike are getting breached. There are the big ones that make all the headlines, like LinkedIn, Twitter and Zappos. But just in the last month there were some significant data breaches, like one at the Florida Department of Juvenile Justice. In this case a mobile device was lost or stolen with 100,000 records containing personally identifiable information (PII). The lesson is that you are not too small to be a target.
Another interesting finding from the report was that most organizations are still using the same technologies to prevent data breaches and network intrusions. This seems counterintuitive. If I’m using something and it’s not working, why continue to use it?
We need to move the conversation to one that assumes you will be breached and determine how to mitigate your risk. You need to assume that your perimeter will be or is already breached. The bad guys are already inside. The New York Times and The Wall Street Journal were recent victims of this problem.
If that’s the case, what are you trying to protect? The information inside your organization. That information is found in databases and documents. It’s important to safeguard your environment from malicious hackers, but many of the data breaches are from inadvertent acts. There are a lot of recent incidents of someone stealing a laptop with sensitive data or having a CD lost in the mail. These problems are from trusted insiders. Protecting the perimeter doesn’t help in this case. You need to protect the data.
You need to encrypt the data inside your databases and use strong authentication methods to ensure that only authorized people can access the information. Granted that some of the recent hacks are sophisticated, but too often basic vulnerabilities are being used to access the data. People using default passwords for admin accounts and keeping passwords in plain text files accessible from the Internet are too common.
The same should apply to documents. You need to encrypt documents with a persistent file-level security policy that lets you control who can access the file. The policy lets you control the document no matter where it is and what format it’s in. If a hacker gets the document, it’s useless to them, since they can’t see what’s inside. They might as well be reading 1s and 0s or an alien language.
It’s time to assume your network perimeter is or will be breached. Make sure that once the bad guys are inside, they can’t access the important information inside your organization. Encrypt the data.
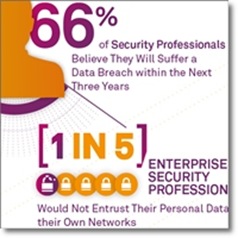
Below is a great infographic with some of the results of the SafeNet survey.


