The Fasoo Data Security Platform is purpose-built for lifecycle control of enterprise-sensitive unstructured data. Sensitive data is comprehensively protected and managed in accordance with corporate governance and regulatory requirements. The platform combines the most advanced data security and management technologies to safeguard sensitive data throughout its lifecycle, regardless of location. Critical sensitive data security and privacy functions are consolidated into a single highly automated sequence of processes.
A seamless connection between processes provides the most effective, efficient, centralized, and automated approach to corporate and regulatory unstructured data governance. The components of the Fasoo Data Security Platform below set us apart from the competition and is why over 2,000 organizations and millions of users trust Fasoo.
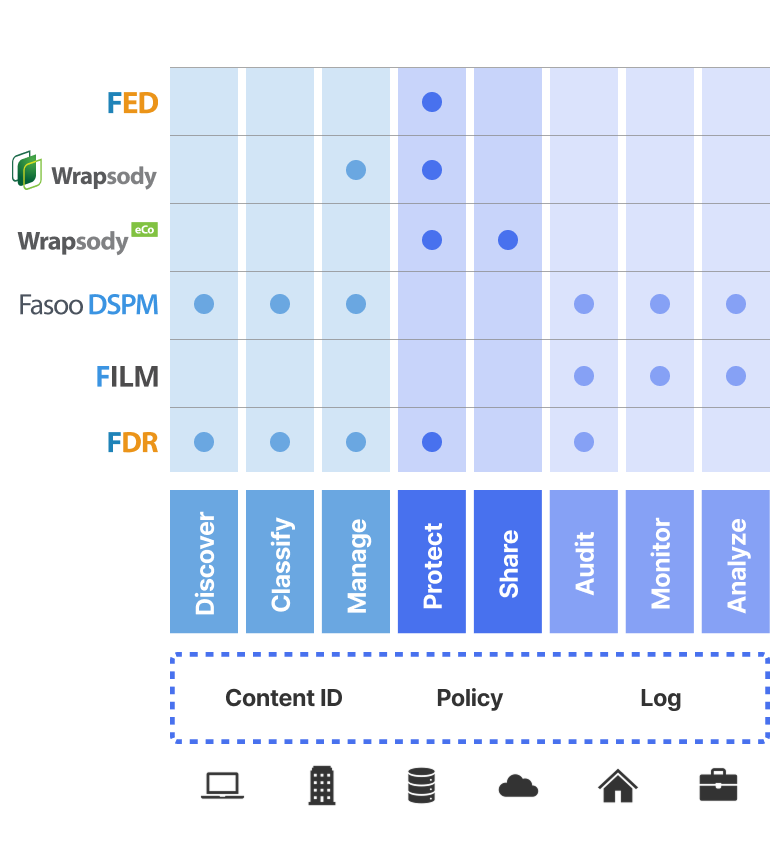

A data governance solution to discover and classify sensitive unstructured data based on its association with people and other characteristics, showing the data’s security vulnerability and dynamically applying security policies on a continuous basis.

The most advanced file-based security solution that allows organizations to protect, control and track sensitive documents to meet the internal and regulatory security requirements during all stages in the document lifecycle.
An information-centric content services platform for data collaboration, management, governance, and protection. Using a persistent ID enables organizations to integrate a core set of functions essential to all applications that touch enterprise unstructured data.

An intuitive and open collaboration solution that lets you securely share, trace, control, and remotely expire access to sensitive content. Content is always protected and under your control, internally and at third parties, with traceability and audit accountability meeting today’s most stringent regulatory compliance requirements.
A user behavior and risk management analytic solution that applies sophisticated rule-based modeling to confidential data to establish normal patterns of behavior. It flags suspicious activities that may indicate elevated levels of risk and can alert management to a potential data breach.

Don't let work-from-home put your sensitive data at risk
Solution
Collaborate securely on sensitive documents using Wrapsody eCo while you work-from-home during the COVID-19 pandemic.

Stop intellectual property theft by encrypting and controlling data
Video
Minimize insider threats by encrypting and controlling sensitive data at the point of creation and improve your overall enterprise security.

Discourage printing sensitive information on home printers
Solution
Block printing of sensitive data in documents on home printers using Fasoo Smart Print while you work-from-home during the COVID-19 pandemic.
Don’t let work-from-home put your sensitive data at risk
Solution
Collaborate securely on sensitive documents using Wrapsody eCo while you work-from-home during the COVID-19 pandemic.
Stop intellectual property theft by encrypting and controlling data
Video
Minimize insider threats by encrypting and controlling sensitive data at the point of creation and improve your overall enterprise security.
Discourage printing sensitive information on home printers
Solution
Block printing of sensitive data in documents on home printers using Fasoo Smart Print while you work-from-home during the COVID-19 pandemic.