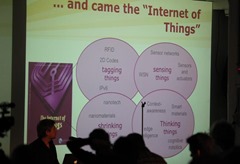
According to Gartner, Inc. by 2020, 25 billion Internet connected “things” will be in use. The Internet of Things “IoT” has rapidly become one of the most used expression across business and technology. IoT, is defined as “a scenario in which objects, animals or people are provided with unique identifiers and the ability to transfer data over a network without requiring human-to-human or human-to-computer interaction.”
Now, how does data security play into this? Well, there are very clear data collection guidelines that companies and public organizations must abide by in the EU, however, there is yet to be a single data protection law comparable to that of the EU. Yet the US has a patchwork system of federal and state laws and regulation that can sometimes overlap. Either way, when it comes to ‘things’ collecting data, there has yet to be a standard guidelines, laws or regulations on securing this data. With a recent study estimating 13 billion ‘things’ collecting data – and that number will nearly double within five years, everyone should be concerned. If this data is not secure, hackers and insider theft could cause catastrophic damage.
It is vital that this data is secured and even more so encrypted in order to avoid not just theft of data but also to avoid data from being deliberately miscommunicated to cause harm by terrorists. This may seem extreme for some, but with recent cyber attacks reported were from state governments and terrorists groups, is it even worth taking our chances not to secure this data?
Although there are some benefits such as smart cities, better healthcare through remote sensors and better ways of targeting consumers for businesses, government and consumers, we are handing over a lot of data without perhaps realizing it.
When we encrypt the data and apply persistent security policies to them automatically, sensitive data is protected regardless of where it is or how it is transmitted. If those that are collecting the data regardless if they are inside or outside of the organization, tried to use it for any other means and tried to open it without the proper authorization, they would be denied access to the data.
The future and promise of the IoT is huge, but so is the potential for security breaches and threat gaps. Every organization that deals with data collected from these IoTs must rethink how to protect these massive amounts of data. By protecting it with data-centric security, this will ensure that data will be secure and consumers will continue to use these ‘things’ for the convenience it was intended to be used for plus the assurance that their data is secure.
Photo credit by: Playing Futures: Applied Nomadology