Under the Foreign Intelligence Surveillance Act (FISA) and the Patriot Act, metadata can be gathered at any time, for any reason, without subpoena, and without suspicion of any crime. If an agency, like the FBI, uncovers information they find interesting, and can claim it’s related to international terrorism, they can get a court order to investigate further. PRISM seems to expand these capabilities.
The concern is that law enforcement and other agencies may start a fishing expedition looking for anything incriminating that has nothing to do with the initial concern. The US Constitution provides protection against unreasonable search and seizure which guards against these types of activities. It’s unclear where these programs stop. Recent reports say the NSA may store everything sent through the Internet for analysis in the future, just in case. Can they indeed go looking through your documents, emails, images and anything else you have stored in the cloud or at that comes through your ISP?
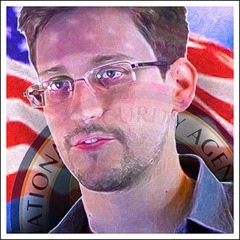
The story brings up two concerns. One is that a government contractor named Edward Snowden leaked information about the PRISM program. The other is the ramifications of the program itself. Protecting your privacy and the security of your business is more important than ever in this climate of uncertainty. Your ISP and cloud provider may have plans to implement email and file-based encryption, but there is no guarantee this will prevent snooping. And how about confidential files inside your organization?
The best way to ensure your privacy and security is to encrypt your sensitive files and email before you share them. Basic encryption is not enough, since it doesn’t control how someone can use your data. Applying a security policy ensures that you can not only control who views your files, but also limit editing, printing and even the ability to take a screen capture. If you suspect a major data breach, you can even revoke access to your files immediately. That removes all access to the data for everyone.
Employees and contractors deliberately or inadvertently sharing sensitive information with unauthorized people can cause major problems. Governments or other organizations having access to your most critical business information can be eliminated by encrypting your files with a persistent security policy that leaves you in control.
Photo credit DonkeyHotey

